Explore the Nintendo Game Pocket and Games

Pocket Heaven was created to provide visitors with up-to-date information on the Nintendo Game Boy Pocket and Game Boy Pocket games. Enjoy hours of entertainment on your Nintendo Game Boy Pocket and visit our website regularly for the latest news, reviews, and updates. What you'll find on Pocket Heaven is a massive selection of Game Boy Pocket games to play. We even list unique casino games that you can play on the latest generations of Nintendo. To get an incredible 50 free spins bonus and play for free, head over to the CaBonusCasino.com site. We'll review the different games available and provide you with tips and tricks to get the most out of your Game Boy Pocket. We welcome you to subscribe to our newsletter for exclusive deals on Nintendo Game Boy Pocket and games.
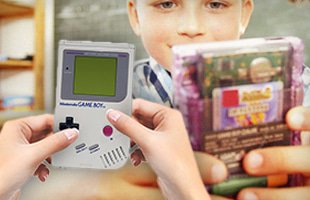
The History of Game Boy
The first Game Boy manufactured was released on the 100th anniversary of Nintendo on April 21, 1989. As the first handheld console in the Game Boy line, the console boasted excellent battery life and rugged hardware which made it incredibly popular. How popular, you ask? Within the first week of the launch of the Game Boy, all 300,000 units of stock were sold. Later, when the Game Boy arrived in the US on July 31, 1989, the entire first shipment of 1 million units was sold within a week. While there were many revisions, the one that stood head and shoulders above the rest is the Nintendo Game Boy Pocket, a smaller, lighter and far more battery efficient ꟷ the two AAA batteries provide approximately 10 hours of gameplay. The Nintendo Game Boy Pocket was released in 1996 and, surprisingly, did not come with a power LED. This was added later due to popular demand.
The Best Game Boy Games
 Tetris: as one of the best-selling games ever invented, Tetris first became available for Game Boy in 1989. Since then, Tetris has been named as Electronic Gaming Monthly's "Greatest Game of All Time". Tetris opened up an exciting world where simplicity and ingenuity came together to produced hours of entertainment. The sound effects and animations of rockets blasting off at the end of each level made the game even more exciting for players.
Tetris: as one of the best-selling games ever invented, Tetris first became available for Game Boy in 1989. Since then, Tetris has been named as Electronic Gaming Monthly's "Greatest Game of All Time". Tetris opened up an exciting world where simplicity and ingenuity came together to produced hours of entertainment. The sound effects and animations of rockets blasting off at the end of each level made the game even more exciting for players.
Super Mario Land: released in 1989, the game offers on the go action by giving players the first full-scale side-scrolling game for other models. The objective in Super Mario Land is to traverse each level and reach one of the exit doors. The exit door at the top of the screen typically transported players to a mini-game where you could win extra lives and power-ups. The black and white visuals in Super Mario Land are just about what you'd expect from a first-generation release, but that's also what makes it so incredibly iconic.
The Legend of Zelda: developed by Nintendo in the 1980s, The Legend of Zelda is an action-adventure video game incorporates puzzle-solving elements and exploration in a fantasy world that inspired a number of spin-offs and an animated television series based on the game. Unique to The Legend of Zelda is the multidirectional moment, allowing players the freedom to explore their surroundings and uncover hidden keys and puzzle pieces to progress through the levels.
Pokémon Red and Blue: the game was developed by Game Freak and provides Game Boy Pocket games with an over-few perspective of the fictional region of Kanto in a quest to become a Pokémon master. Players are required to defeat gym leaders, and then face-off against the top trainers in the land called the Elite Four. Another objective is to complete the Pokédex by capturing all 150 characters.
One interesting fact about Nintendo is that there are many casino slots games based on their game franchises, which just shows the popularity and cult status of Nintendo. So today, you can play real money Mario and Zelda slots, with the life-changing jackpot prizes. Playing your favorite characters and winning money, we have to admit that it is an exciting mix for all Nintendo fans. Since you are probably intrigued, you can try these games for free before you decide to invest your own money, by using the no deposit casino bonuses from online Canadian casinos that you can find at https://sansdepotquebecois.ca/. Try your luck, you have nothing to lose!
Popular Nintendo Game Boy Categories
Pocket Heaven offers in-depth information on Game Boy Pocket Games. These include action, adventure, puzzle, fantasy, and even casino games. We'll continue to add information on the different types of games you can play as well as the types of games that can be played on each different type of console: Nintendo Game Boy Pocket, Game Boy Color, Game Boy Light, and Game Boy Advance. These include classics such as poker, which you can start playing by visiting https://pokerler.com for more information.
